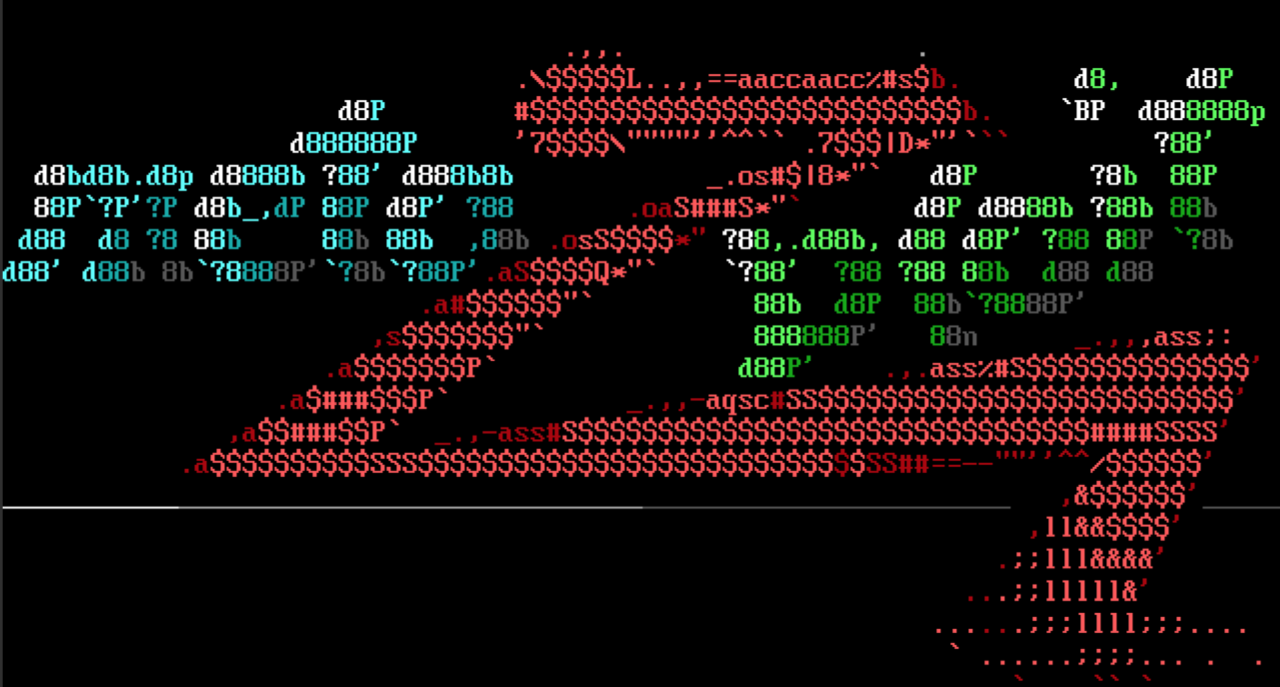
ESC15: EKUwu
AD CS continues to be a popular target for penetration testers and security practitioners. The latest escalation technique (hence the the ESC in ESC15) was discovered by Justin Bollinger with details being released just last week. This latest configuration flaw has common issuance requirements to other ESC flaws
ESC15: EKUwu
AD CS continues to be a popular target for penetration testers and security practitioners. The latest escalation technique (hence the the ESC in ESC15) was discovered by Justin Bollinger with details being released just last week. This latest configuration flaw has common issuance requirements to other ESC flaws such as requiring no authorized signatures or manager approval. Additionally, templates must be schema version 1 which enables an attacker to craft a signing request with a custom set of EKU OIDs which will be present in the issued certificate. By overriding the OIDs, the template can be used in a few ways with the most useful being as a certificate enrollment agent. With a valid enrollment agent certificate, a user can issue certificates for other users which, when combined with the builtin “User” certificate, can enable Kerberos authentication to a wide variety of services.
This week’s release of Metasploit has added support to our existing AD CS related modules for identifying and exploiting ESC15.
The auxiliary/admin/ldap/ad_cs_cert_template module can be used along with the new esc15_template to create a vulnerable certificate or (by leveraging ESC4) update an existing certificate to be vulnerable to ESC15.
The auxiliary/gather/ldap_esc_vulnerable_cert_finder module has been updated to identify vulnerable certificate templates.
The auxiliary/admin/dcerpc/icpr_cer module has been updated with the new ADD_CERT_APP_POLICY option to enable users to add EKUs by OID, thus enabling exploitation of ESC15.
For exploitation steps, see the ESC15 section of our AD CS documentation.
New module content (2)
WordPress WP Fastest Cache Unauthenticated SQLi (CVE-2023-6063)
Authors: Alex Sanford, Julien Voisin, and Valentin Lobstein
Type: Auxiliary
Pull request: #19473 contributed by Chocapikk
Path: scanner/http/wp_fastest_cache_sqli
AttackerKB reference: CVE-2023-6063
Description: This adds an auxiliary module to dump user credentials through a Time-based SQL injection present in WP Fastest Cache Plugin <= 1.2.2.
BYOB Unauthenticated RCE via Arbitrary File Write and Command Injection (CVE-2024-45256, CVE-2024-45257)
Authors: Valentin Lobstein and chebuya
Type: Exploit
Pull request: #19485 contributed by Chocapikk
Path: unix/webapp/byob_unauth_rce
AttackerKB reference: CVE-2024-45257
Description: This adds an exploit module for BYOB unauthenticated RCE (CVE-2024-45256, CVE-2024-45257).
Enhanced Modules (2)
Modules which have either been enhanced, or renamed:
- #19482 from Chocapikk - The module allows users to select between the two vulnerabilities (c_only_fields for CVE-2024-8522 and c_fields for CVE-2024-8529) and includes options such as specifying the number of rows to retrieve (COUNT).
- #19538 from zeroSteiner - This adds support for ESC15 to various AD CS related modules.
Enhancements and features (6)
- #19108 from smashery - Adds a new API,
create_process, which supports creating processes against an open session from an array of args, rather than from a commandline string that needs to go through a subshell. This pull request also fixes multiple module compatibility issues across different session types, i.e. targeting Meterpreter/PowerShell/Cmd/Unix sessions should now behave consistently when running post exploitation and local privilege escalation modules that execute processes. - #19497 from Chocapikk - This adds an helper library for the development of Wordpress SQLi modules.
- #19539 from smashery - This adds functionality to keep the new LDAP sessions alive beyond a server's idle timeout.
- #19540 from smashery - Update Metasploit's HTTP request User Agent strings for October 2024.
- #19549 from zeroSteiner - This pull request includes multiple fixes and improvements to the Meterpreter payloads. zeroSteiner fixed a
stdapi_fs_ls: Operation failed: 1error when running thelscommand with the Java Meterpreter. cdelafuente-r7 has updated the Java Meterpreter payload to now run on newer OpenJDK versions on Alpine Linux hosts. wolfcod has made improvements for running the C Meterpreter on Windows XP machines when creating remote threads, as well as fixing a memory leak in thesysinfocommand. - #19561 from cdelafuente-r7 - Updates the
gather/ldap_esc_vulnerable_cert_findermodule to now register the detected vulnerabilities into the Metasploit database if it is currently active.
Bugs fixed (2)
- #19495 from cdelafuente-r7 - Fixes an edgecase crash in the
admin/kerberos/get_ticketmodule when the supplied cert_file contained a subjectAltName extension with an unexpected value present. - #19563 from adfoster-r7 - Updates
exploits/linux/http/metabase_setup_token_rceto support older versions.
Documentation
You can find the latest Metasploit documentation on our docsite at docs.metasploit.com.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate
and you can get more details on the changes since the last blog post from
GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest.
To install fresh without using git, you can use the open-source-only Nightly Installers or the
commercial edition Metasploit Pro
Source: Rapid7
Source Link: https://blog.rapid7.com/2024/10/18/metasploit-weekly-wrap-up-10-18-2024/