
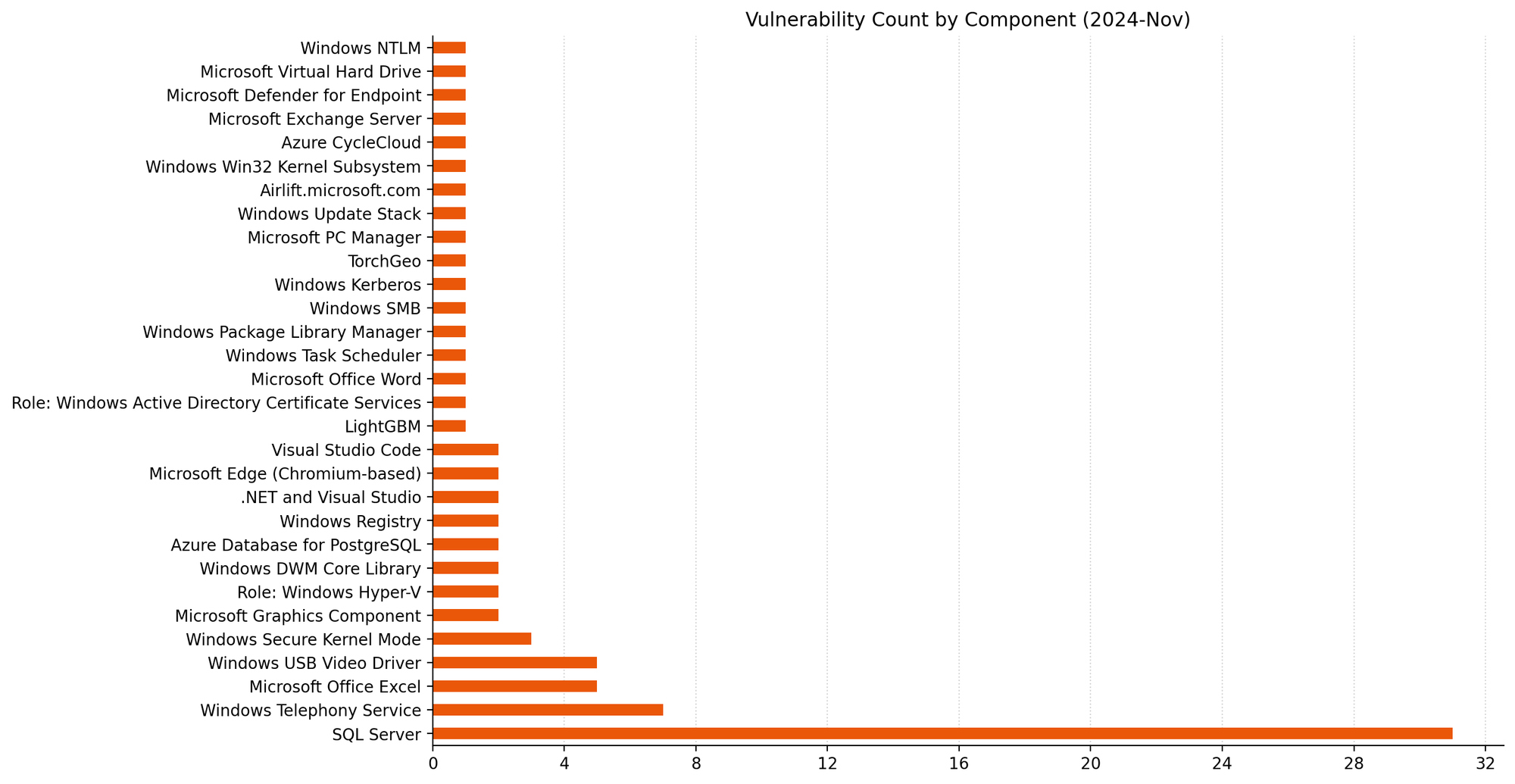
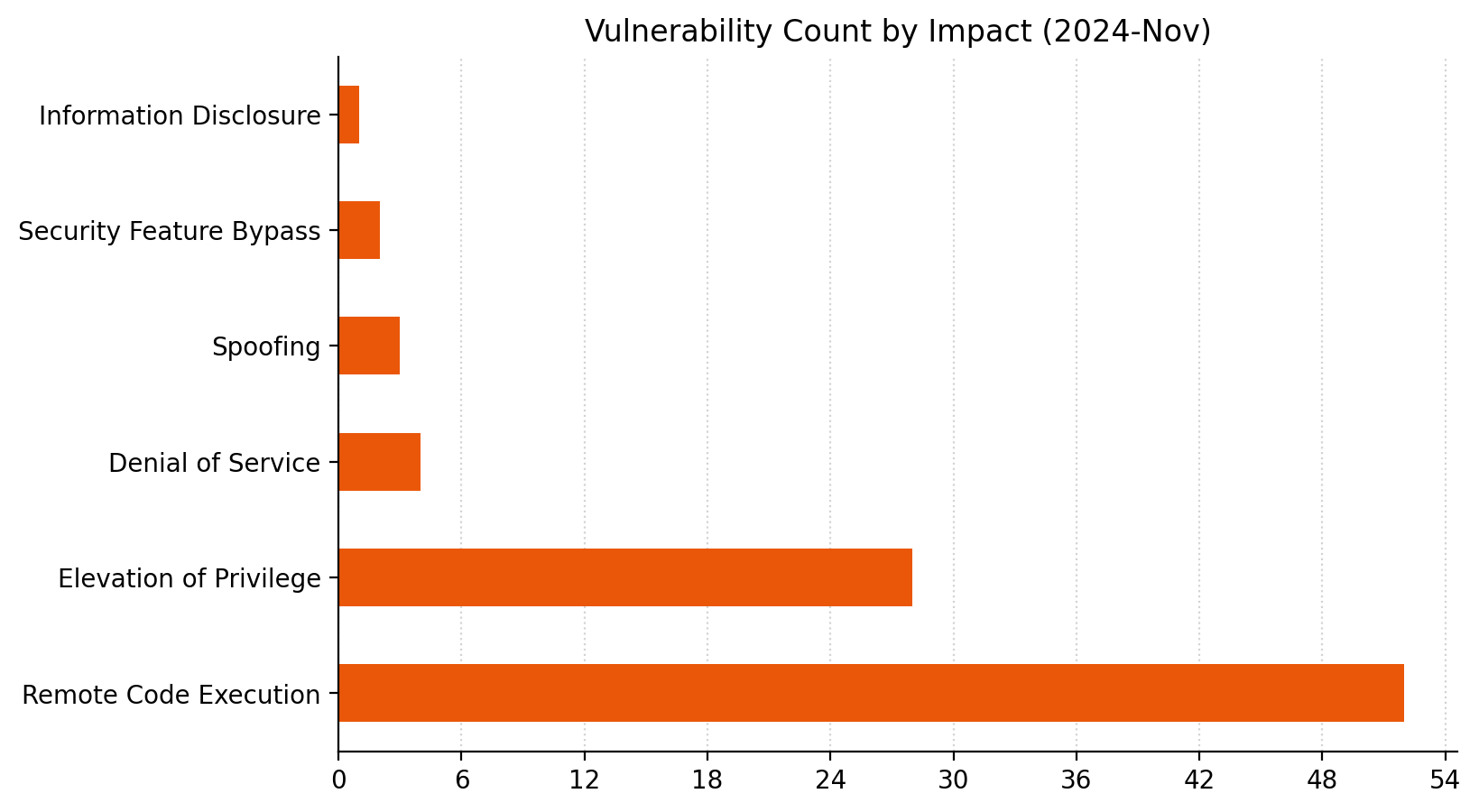
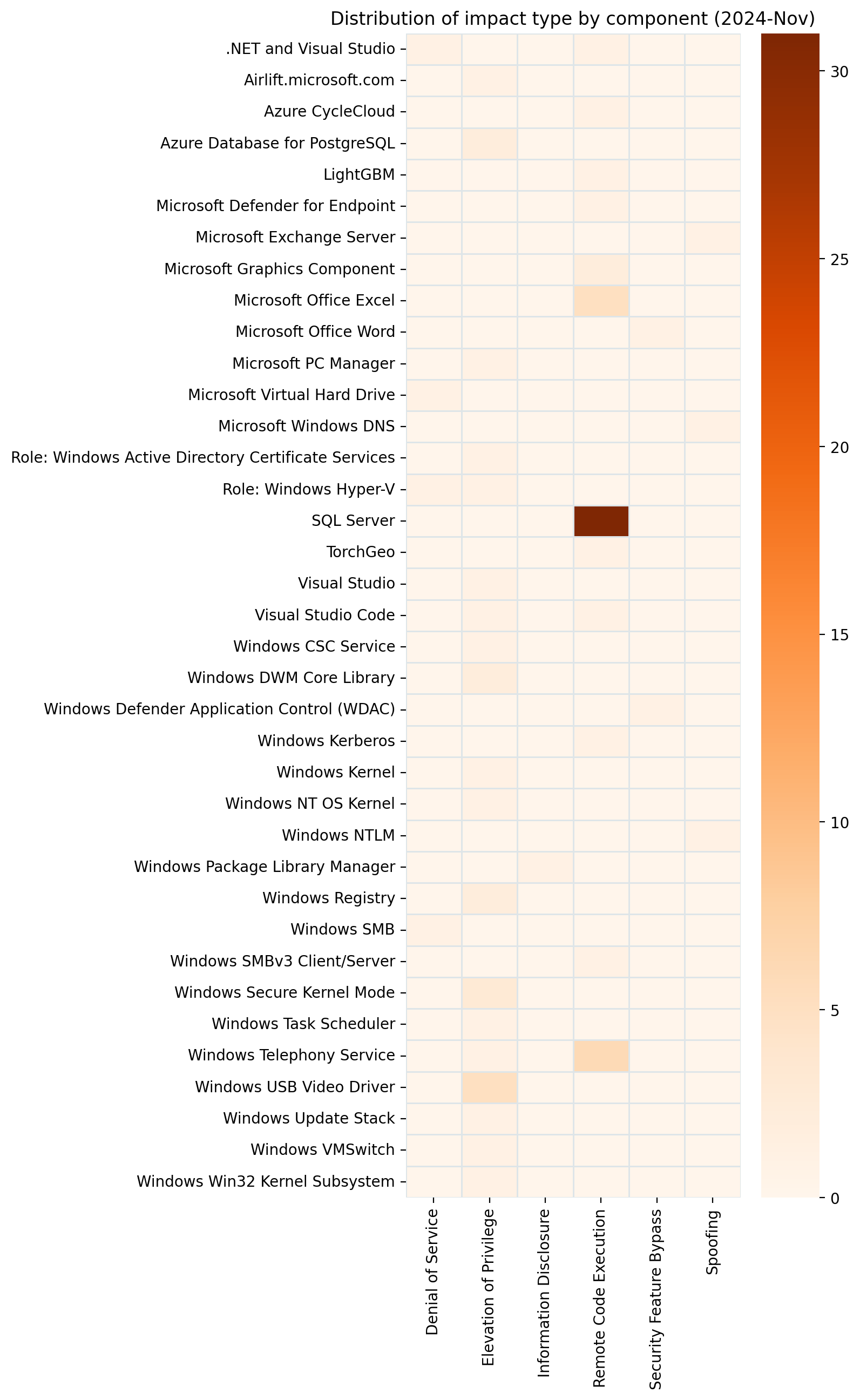
Microsoft is addressing 90 vulnerabilities this November 2024 Patch Tuesday. Microsoft has evidence of in-the-wild exploitation and/or public disclosure for four of the vulnerabilities published today, although as with last month’s batch, it does not evaluate any of these zero-day vulnerabilities as critical severity (yet). Of those four, Microsoft lists two as exploited in the wild, and both of these are now listed on CISA KEV. Microsoft is aware of some level of public disclosure for three. Microsoft is also patching two further critical remote code execution (RCE) vulnerabilities today. Two browser vulnerabilities have already been published separately this month, and are not included in the total.
Active Directory Certificate Service: zero-day EoP aka EKUwu
CVE-2024-49019 describes an elevation of privilege vulnerability in Active Directory Certificate Services. While the vulnerability only affects assets with the Windows Active Directory Certificate Services role, an attacker who successfully exploits this vulnerability could gain domain admin privileges, so that doesn’t offer much comfort. Unsurprisingly, given the potential prize for attackers, Microsoft assesses future exploitation as more likely. Vulnerable PKI environments are those which include published certificates created using a version 1 certificate template with the source of subject name set to "Supplied in the request" and Enroll permissions granted to a broader set of accounts. Microsoft does not obviously provide any means of determining the certificate template version used to create a certificate, although the advisory does offer recommendations for anyone hoping to secure certificate templates.
There is a significant history of research and exploitation of Active Directory Certificate Services, including the widely-discussed Certified Pre-Owned series, and the discovering researchers have now added further to that corpus, tagging CVE-2024-49019 as ESC15. In keeping with another long-standing infosec tradition, the researcher has provided a fun celebrity vulnerability name — in this case, EKUwu, a portmanteau of EKU (Extended Key Usage) and UwU, an emoticon representing a cute face — as part of their detailed and insightful write-up.
MSHTML: zero-day NTLMv2 hash disclosure
Given the CVSSv3 base score of 6.0, one might almost be forgiven for overlooking CVE-2024-43451, which describes an NTLM hash disclosure spoofing vulnerability in the MSHTML platform which powered Internet Explorer. However, public disclosure and in-the-wild exploitation are always worth a look. Although exploitation requires that the user interact with a malicious file, a successful attacker receives the user’s NTLMv2 hash, and can then use that to authenticate as the user.
Microsoft has arguably scored CVE-2024-43451 correctly according to the CVSSv3.1 specification. However, although the Microsoft CVSSv3 vector describes an impact only to confidentiality, if an attacker can authenticate as the user post-exploitation, a further potential for subsequent impact to integrity and availability now exists; if we take that potential indirect effect into account, the CVSSv3 base score would look more like 8.8, which is the sort of number where alarm bells typically start ringing for many defenders. As a further sting in the tail, the advisory FAQ describes the required user interaction as minimal: left click, right click, or even the highly non-specific “performing an action other than opening or executing [the file]”. There’s certainly the potential for a long tail of exploitation here, especially in environments with more relaxed patching cadence.
The complete Windows catalog from Server 2025 and Windows 11 24H2 all the way back to Server 2008 receives patches for CVE-2024-43451. As Rapid7 has previously noted, MSHTML (also known as Trident) is still fully present in Windows — and unpatched assets are thus vulnerable — regardless of whether or not a Windows asset has Internet Explorer 11 disabled.
Exchange: zero-day sender spoofing
It’s been a few months since we’ve seen any security patches for Exchange, but the streak is now broken with a zero-day vulnerability. Mailserver admins should be paying attention to CVE-2024-49040, which is a publicly disclosed spoofing vulnerability. The specific weakness is CWE-451: User Interface (UI) Misrepresentation of Critical Information, which is often associated with phishing attacks, as well as browser vulnerabilities, and can describe a wide range of misdeeds, from visual truncation and UI overlay to homograph abuse. Microsoft does not yet claim knowledge of in-the-wild exploitation.
The advisory for CVE-2024-49040 hints that post-patching actions may be required for remediation of CVE-2024-49040, and links to further information in a separate article titled “Exchange Server non-RFC compliant P2 FROM header detection”. A careful read of the article doesn’t appear to list any mandatory post-patching actions; instead, there is an optional extra mitigation strategy action around Exchange Transport Rules, as well as an encouragingly detailed explanation of the protection offered by today’s patches. The article showcases that an Exchange-connected email client such as Outlook might display a forged sender as if it were legitimate, which we can all agree is not a good outcome. Attackers don’t have to look far to find other vulnerabilities to chain with this one, since today’s sibling zero-day vulnerability CVE-2024-43451 is certainly an option. On the other hand, let’s take a moment to appreciate the Exchange team’s blog title: “You Had Me at EHLO”.
Patches for CVE-2024-49040 are available for Exchange 2019 CU13 and CU14, as well as Exchange 2016 CU23. It’s worth remembering that both Exchange 2016 and 2019 have an extended end date of 2025-10-14, which is now less than a year away; this despite the fact that the successor for 2016 and 2019, which Microsoft is unsubtly branding as Exchange Server Subscription Edition, isn’t due for release until early in 2025 Q3. Many admins would no doubt prefer a longer upgrade window.
The researcher who reported CVE-2024-49040 also discovered a means to impersonate Microsoft corporate email accounts earlier this year, but went public with his findings after Microsoft dismissed his report; it appears that the relationship has been at least somewhat repaired.
Task Scheduler: zero-day EoP (but not SYSTEM)
Windows Task Scheduler facilitates all sorts of useful outcomes, and if you’re a threat actor, it now offers one more: elevation of privilege via CVE-2024-49039. Microsoft is aware of exploitation in the wild. Given the low attack complexity and low privileges requirement, no requirement for user interaction, high impact across the CIA triad, and changed scope, it’s no surprise that the CVSSv3 base score comes out as a relatively zesty 8.8. However, Windows elevation of privilege vulnerabilities are always most exciting for attackers when they lead directly to SYSTEM privileges, but that’s not the case here. The attacker in this scenario starts out in a low-privileged AppContainer sandbox, and exploitation via a malicious app provides medium integrity level privileges, which is the same as a regular non-administrative user on the system. Still, every step forward for a threat actor is a step back for defenders.
.NET: critical RCE
This month brings patches for CVE-2024-43498, a critical RCE in .NET 9.0 with a CVSSv3 base score of 9.8, which is so seldom a harbinger of good news. Exploitation might mean compromise of a desktop application by loading a malicious file, but most concerningly could also describe RCE in the context of a vulnerable .NET webapp via a specially crafted request. Microsoft assesses exploitation as less likely, but there’s nothing on the advisory which obviously supports that assessment, since this is a low-complexity network attack which requires neither privileges nor user interaction. CVE-2024-43498 is surely worthy of immediate patching. It’s also never a bad idea to review other options for protection, especially for internet-exposed services.
Kerberos: critical RCE
The advisory for CVE-2024-43639 describes a critical RCE in Kerberos with a CVSSv3 base score of 89.8, although not in great detail. The FAQ explains that an unauthenticated attacker could use a specially crafted application to leverage a cryptographic protocol vulnerability in Windows Kerberos to perform remote code execution against the target, but without providing much information about the target or the precise context of code execution. The only safe assumption here is that code execution is in a highly-privileged context on a server which handles key authentication tasks. Patch accordingly.
Microsoft lifecycle update
In Microsoft lifecycle news, the most notable change is the arrival of Windows Server 2025 as a General Availability product at the start of November. Microsoft has announced a number of new features in Server 2025, which we will look forward to discussing in more detail in future editions of this blog.
At the other end of the lifecycle continuum, .NET 6.0 receives its final scheduled updates today; as .NET 6.0 is/was a Long Term Support (LTS) version, and .NET 7.0 is already beyond end of life, the only current upgrade path is to .NET 8.0.
Summary charts
Summary tables
Apps vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49051 | Microsoft PC Manager Elevation of Privilege Vulnerability | No | No | 7.8 |
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43602 | Azure CycleCloud Remote Code Execution Vulnerability | No | No | 9.9 |
| CVE-2024-49056 | Airlift.microsoft.com Elevation of Privilege Vulnerability | No | No | 7.3 |
| CVE-2024-49042 | Azure Database for PostgreSQL Flexible Server Extension Elevation of Privilege Vulnerability | No | No | 7.2 |
| CVE-2024-43613 | Azure Database for PostgreSQL Flexible Server Extension Elevation of Privilege Vulnerability | No | No | 7.2 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-10827 | Chromium: CVE-2024-10827 Use after free in Serial | No | No | N/A |
| CVE-2024-10826 | Chromium: CVE-2024-10826 Use after free in Family Experiences | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43498 | .NET and Visual Studio Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-49050 | Visual Studio Code Python Extension Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43499 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-49049 | Visual Studio Code Remote Extension Elevation of Privilege Vulnerability | No | No | 7.1 |
| CVE-2024-49044 | Visual Studio Elevation of Privilege Vulnerability | No | No | 6.7 |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-43639 | Windows Kerberos Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-43627 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43628 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43620 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43621 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43622 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43635 | Windows Telephony Service Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49046 | Windows Win32 Kernel Subsystem Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43626 | Windows Telephony Service Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43641 | Windows Registry Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43623 | Windows NT OS Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43644 | Windows Client-Side Caching Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43636 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-49019 | Active Directory Certificate Services Elevation of Privilege Vulnerability | No | Yes | 7.8 |
| CVE-2024-43452 | Windows Registry Elevation of Privilege Vulnerability | No | No | 7.5 |
| CVE-2024-43450 | Windows DNS Spoofing Vulnerability | No | No | 7.5 |
| CVE-2024-43634 | Windows USB Video Class System Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-43637 | Windows USB Video Class System Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-43638 | Windows USB Video Class System Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-43643 | Windows USB Video Class System Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-43449 | Windows USB Video Class System Driver Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-43451 | NTLM Hash Disclosure Spoofing Vulnerability | Yes | Yes | 6.5 |
| CVE-2024-38203 | Windows Package Library Manager Information Disclosure Vulnerability | No | No | 6.2 |
Mariner System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-5535 | OpenSSL: CVE-2024-5535 SSL_select_next_proto buffer overread | No | No | 9.1 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49031 | Microsoft Office Graphics Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49032 | Microsoft Office Graphics Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49026 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49027 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49028 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49029 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49030 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49033 | Microsoft Word Security Feature Bypass Vulnerability | No | No | 7.5 |
Open Source Software vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49048 | TorchGeo Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-43598 | LightGBM Remote Code Execution Vulnerability | No | No | 7.5 |
SQL Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38255 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43459 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-43462 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48994 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48995 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48996 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48993 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48997 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48998 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-48999 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49000 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49001 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49002 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49003 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49004 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49005 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49007 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49006 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49008 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49009 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49010 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49011 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49012 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49013 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49014 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49015 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49016 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49017 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49018 | SQL Server Native Client Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-49043 | Microsoft.SqlServer.XEvent.Configuration.dll Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-49021 | Microsoft SQL Server Remote Code Execution Vulnerability | No | No | 7.8 |
Server Software vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49040 | Microsoft Exchange Server Spoofing Vulnerability | No | Yes | 7.5 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-49039 | Windows Task Scheduler Elevation of Privilege Vulnerability | Yes | No | 8.8 |
| CVE-2024-43624 | Windows Hyper-V Shared Virtual Disk Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-43447 | Windows SMBv3 Server Remote Code Execution Vulnerability | No | No | 8.1 |
| CVE-2024-43625 | Microsoft Windows VMSwitch Elevation of Privilege Vulnerability | No | No | 8.1 |
| CVE-2024-43530 | Windows Update Stack Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43640 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43630 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43629 | Windows DWM Core Library Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-43642 | Windows SMB Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-43631 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | No | 6.7 |
| CVE-2024-43646 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | No | 6.7 |
| CVE-2024-43645 | Windows Defender Application Control (WDAC) Security Feature Bypass Vulnerability | No | No | 6.7 |
| CVE-2024-43633 | Windows Hyper-V Denial of Service Vulnerability | No | No | 6.5 |
| CVE-2024-38264 | Microsoft Virtual Hard Disk (VHDX) Denial of Service Vulnerability | No | No | 5.9 |
Source: Rapid7
Source Link: https://blog.rapid7.com/2024/11/12/patch-tuesday-november-2024/