Frequently asked questions about a zero-day vulnerability in Fortinet’s FortiManager that has reportedly been exploited in the wild.
Background
The Tenable Security Response Team (SRT) has compiled this blog to answer Frequently Asked Questions (FAQ) regarding a zero-day vulnerability in Fortinet’s FortiManager.
FAQ
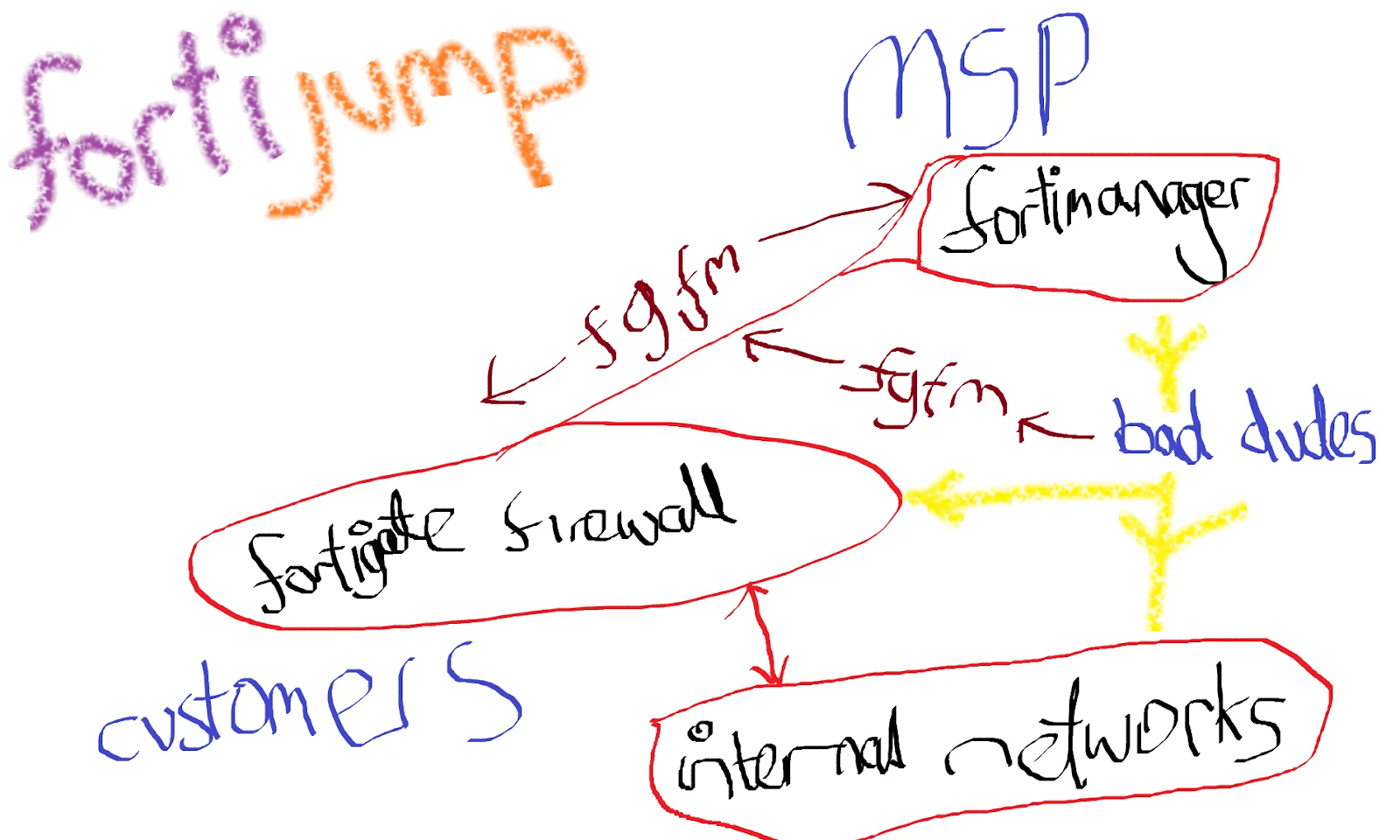
What is FortiJump?
FortiJump is a name given to a zero-day vulnerability in the FortiGate-FortiManager (FGFM) protocol in Fortinet’s FortiManager and FortiManager Cloud. It was named by security researcher Kevin Beaumont in a blog post on October 22. Beaumont also created a logo for FortiJump.
What are the vulnerabilities associated with FortiJump?
On October 23, Fortinet published an advisory (FG-IR-24-423) for FortiJump, assigning a CVE identifier for the flaw.
What is CVE-2024-47575?
CVE-2024-47575 is a missing authentication vulnerability in the FortiGate to FortiManager (FGFM) daemon (fgfmsd) in FortiManager and FortiManager Cloud.
How severe is CVE-2024-47575?
Exploitation of FortiJump could allow an unauthenticated, remote attacker using a valid FortiGate certificate to register unauthorized devices in FortiManager. Successful exploitation would grant the attacker the ability to view and modify files, such as configuration files, to obtain sensitive information, as well as the ability to manage other devices.
Obtaining a certificate from a FortiGate device is relatively easy:/pblockquote class=reddit-embed-bq data-embed-height=377pa href=https://www.reddit.com/r/fortinet/comments/1g9bxfk/comment/lt72xjd/Comment/abrby from discussionbrina href=https://www.reddit.com/r/fortinet/fortinet/a/p/blockquotepnbsp;/ppAccording to a href=https://www.shodan.io/search?query=port%3A541+xaburesults from Shodan/u/a, there are nearly 60,000 FortiManager devices that are internet-facing, including over 13,000 in the United States, over 5,800 in China, nearly 3,000 in Brazil and 2,300 in India:/pimg src=https://www.tenable.com/sites/default/files/images/blog/2009fd1c-5bc4-42a6-9839-3decd7b4c7b1.png alt=Shodan search results for Fortinet FortiManager devices that are internet-facing. width=449 height=666 referrerpolicy=no-referrer loading=lazypstrongWhen was FortiJump first disclosed?/strong/ppThere were reports on Reddit that Fortinet proactively notified customers using FortiManager about the flaw ahead of the release of patches, though some customers say they never received any notifications. Beaumont a href=https://cyberplace.social/@GossiTheDog/113299762582288860uposted a warning to Mastodon on October 13/u/a:/pblockquote class=mastodon-embed data-embed-url=https://cyberplace.social/@GossiTheDog/113299762582288860/embeda href=https://cyberplace.social/@GossiTheDog/113299762582288860 target=_blank/adiva href=https://cyberplace.social/@GossiTheDog/113299762582288860 target=_blankPost by @[email protected]/a/divdiva href=https://cyberplace.social/@GossiTheDog/113299762582288860 target=_blankView on Mastodon/a/div/blockquotepnbsp;/ppstrongWas this exploited as a zero-day?/strong/ppYes, according to both Beaumont and Fortinet, FortiJump has been exploited in the wild as a zero-day./ppstrongWhich threat actors are exploiting FortiJump?/strong/ppNo specific threat actors have been attributed to the exploitation of FortiJump, though reports suggest the flaw has been exploited by nation-state groups as part of cyber espionage activity./ppstrongIs there a proof-of-concept (PoC) available for this vulnerability/these vulnerabilities?/strong/ppAs of October 23, there are no public proof-of-concept exploits available for FortiJump./ppstrongAre patches or mitigations available for FortiJump?/strong/ppThe following table contains a list of affected products, versions and fixed versions./pdiv class=table-responsivetable class=tabletheadtrthstrongAffected Product/strong/ththstrongAffected Versions/strong/ththstrongFixed Version/strong/th/tr/theadtbodytrtdFortiManager 6.2/tdtd6.2.0 through 6.2.12/tdtdUpgrade to 6.2.13 or above/td/trtrtdFortiManager 6.4/tdtd6.4.0 through 6.4.14/tdtdUpgrade to 6.4.15 or above/td/trtrtdFortiManager 7.0/tdtd7.0.0 through 7.0.12/tdtdUpgrade to 7.0.13 or above/td/trtrtdFortiManager 7.2/tdtd7.2.0 through 7.2.7/tdtdUpgrade to 7.2.8 or above/td/trtrtdFortiManager 7.4/tdtd7.4.0 through 7.4.4/tdtdUpgrade to 7.4.5 or above/td/trtrtdFortiManager 7.6/tdtd7.6.0/tdtdUpgrade to 7.6.1 or above/td/trtrtdFortiManager Cloud 6.4/tdtd6.4 all versions/tdtdMigrate to a fixed release/td/trtrtdFortiManager Cloud 7.0/tdtd7.0.1 through 7.0.12/tdtdUpgrade to 7.0.13 or above/td/trtrtdFortiManager Cloud 7.2/tdtd7.2.1 through 7.2.7/tdtdUpgrade to 7.2.8 or above/td/trtrtdFortiManager Cloud 7.4/tdtd7.4.1 through 7.4.4/tdtdUpgrade to 7.4.5 or above/td/trtrtdFortiManager Cloud 7.6/tdtdNot affected/tdtdNot Applicable/td/tr/tbody/table/divpFortinet’s advisory provides workarounds for specific impacted versions if patching is not feasible. These include blocking unknown devices from attempting to register to FortiManager, creating IP allow lists of approved FortiGate devices that can connect to FortiManager and the creation of custom certificates. Generally speaking, it is advised to ensure FGFM is not internet-facing./ppstrongHas Tenable released any product coverage for these vulnerabilities?/strong/ppA list of Tenable plugins for this vulnerability can be found on the individual CVE page for a href=https://www.tenable.com/cve/CVE-2024-47575/pluginsuCVE-2024-47575/u/a as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our a href=https://www.tenable.com/plugins/pipelineuPlugins Pipeline/u/a./ph3Get more information/h3ullia href=https://doublepulsar.com/burning-zero-days-fortijump-fortimanager-vulnerability-used-by-nation-state-in-espionage-via-msps-c79abec59773uBurning Zero Days: FortiJump FortiManager vulnerability used by nation state in espionage via MSPs/u/a/lilia href=https://www.fortiguard.com/psirt/FG-IR-24-423uFortiGuard Labs PSIRT FG-IR-24-423 Advisory/u/a/li/ulpemstrongJoin /strong/ema href=https://community.tenable.com/s/group/0F9f2000000fyxyCAA/cyber-exposure-alertsemstronguTenable's Security Response Team/u/strong/em/aemstrong on the Tenable Community./strong/embremstrongLearn more about /strong/ema href=https://www.tenable.com/products/tenable-oneemstronguTenable One/u/strong/em/aemstrong, the Exposure Management Platform for the modern attack surface./strong/em/p
img src=https://www.tenable.com/sites/default/files/images/articles/blog-tenable-research-advisory-high-FAQ_7.jpg /
The post CVE-2024-47575: Frequently Asked Questions About FortiJump Zero-Day in FortiManager and FortiManager Cloud appeared first on Security Boulevard.
Satnam Narang, Rody Quinlan, Scott Caveza
Source: Security Boulevard
Source Link: https://securityboulevard.com/2024/10/cve-2024-47575-frequently-asked-questions-about-fortijump-zero-day-in-fortimanager-and-fortimanager-cloud/