
Microsoft is addressing 88 vulnerabilities this August 2024 Patch Tuesday. Microsoft has evidence of in-the-wild exploitation and/or public disclosure for ten of the vulnerabilities published today, which is significantly more than usual. At time of writing, all six of the known-exploited vulnerabilities patched today are listed on CISA KEV. Microsoft is also patching five critical remote code execution (RCE) vulnerabilities today. 11 browser vulnerabilities have already been published separately this month, and are not included in the total.
Patch Tuesday watchers will know that today’s haul of four publicly-disclosed vulnerabilities and six further exploited-in-the-wild vulnerabilities is a much larger batch than usual. We’ll first address those vulnerabilities where public disclosure exists but no patch is available: the noteworthy Windows OS downgrade attacks disclosed at Black Hat last week. We’ll then examine those vulnerabilities published today which Microsoft knows to be exploited in the wild already, and then take a look at the other publicly-disclosed vulnerabilities published this month.
Windows Update: 50% patched zero-day Downdate attack
First things first: what if your patched Windows asset suddenly wasn’t patched, up to and including the hypervisor? That was the question asked and answered in a Black Hat talk by SafeBreach last week. In response, Microsoft has published two vulnerabilities. Microsoft was first notified of these vulnerabilities back in February 2024, and the advisories concede that the Black Hat talk was “appropriately coordinated with Microsoft.”
CVE-2024-38202 describes an elevation of privilege vulnerability in the Windows Update Stack, and exploitation requires that an attacker convinces an administrative user to perform a system restore — unusual, certainly, but social engineers can accomplish many things. Microsoft optimistically assesses exploitation of this vulnerability as less likely. The advisory does not explain how a user with basic privileges can modify the target asset’s System directory, which is required to plant the malicious system restore files, although the SafeBreach write-up does explain the flaw in significant detail. No patch is yet available, although the advisory states that a security update to mitigate this threat is under development. Microsoft provides several recommended actions, which do not mitigate the vulnerability, but can at least provide additional barriers to exploitation and put in place some useful additional visibility of the attack surface and exploitation attempts. One possible outcome of exploitation is that an attacker could modify the integrity and repair utility so that it will no longer detect corruptions in Windows system files.
CVE-2024-21302 is the second half of the downgrade attack pair discovered by SafeBreach. Exploitation allows an attacker with administrator privileges to replace updated Windows system files with older versions and thus reintroduce vulnerabilities to Virtualization-based security (VBS). Patches are available; however, defenders must note that the patch does not automatically remediate assets, but instead delivers an opt-in Microsoft-signed revocation policy, which brings with it the risk of a boot loop if applied and then improperly reverted. Significant guidance is available under KB5042562: Guidance for blocking rollback of Virtualization-based Security (VBS) related security updates.
Windows WinSock: zero-day EoP
Moving on to known-exploited vulnerabilities: the Windows Ancillary Function Driver for WinSock receives a patch for exploited-in-the-wild elevation of privilege vulnerability CVE-2024-38193. Successful exploitation is via a use-after-free memory management bug, and could lead to SYSTEM privileges. The advisory doesn’t provide further clues, but with existing in-the-wild exploitation, low attack complexity, no user interaction involved, and low privileges required, this is one to patch immediately to keep malware at bay.
Windows Power Dependency Coordinator: zero-day EoP
While we’re looking at exploited-in-the-wild, use-after-free vulnerabilities with minimalist advisories: CVE-2024-38107 also leads to SYSTEM privileges via abuse of the Windows Power Dependency Coordinator, which allows Windows computers to wake almost instantly from sleep. Of course, nothing comes for free: this vulnerability requires no user interaction, has low attack complexity, and requires low privileges. Patch all your Windows assets sooner rather than later.
Windows Kernel: zero-day EoP
Still on the topic of exploited-in-the-wild, elevation-to-SYSTEM vulnerabilities: CVE-2024-38106 requires an attacker to win a race condition which falls under CWE-591: Sensitive Data Storage in Improperly Locked Memory. Although the advisory for CVE-2024-38106 does not provide further detail, a reasonable assumption here might be that the vulnerability could be similar to CVE-2023-36403, where exploitation relies on a flaw in the way the Windows kernel handles locking for registry virtualization, which allows Windows to redirect globally-impactful registry read/write operations to per-user locations to support legacy applications which are not UAC-compatible. Curiously, Windows Server 2012 does not receive a patch for CVE-2024-38106, so either the vulnerability was introduced in a later codebase, or Microsoft is hoping that attackers won’t notice.
Windows SmartScreen: zero-day MotW bypass
CVE-2024-38213 describes a Mark of the Web (MotW) security bypass vulnerability in all current Windows products. An attacker who convinces a user to open a malicious file could bypass SmartScreen, which would normally warn the user about files downloaded from the internet, which Windows would otherwise have tagged with MotW. CVE-2024-38213 likely offers less utility to attackers than a broadly-similar SmartScreen bypass published in February 2024, since unlike today’s offering, the advisory for CVE-2024-21351 also described the potential for code injection into SmartScreen itself. The lower CVSSv3 base score for CVE-2024-21351 reflects that difference.
Edge Internet Explorer mode: zero-day EoP
Although Edge RCE vulnerability CVE-2024-38178 is already known to be exploited in the wild, it likely won’t be top of anyone’s list of greatest concerns this month. The advisory clarifies that successful exploitation would require the attacker to not only convince a user to click a malicious link, but also to first prepare the target asset so that it uses Edge in Internet Explorer Mode. IE Mode provides backwards-compatibility functionality so that users can view legacy websites which rely on the fascinating idiosyncrasies of Internet Explorer; such sites are often served by enterprise legacy web applications, which goes a long way to explaining Microsoft’s continued motivation to keep Internet Explorer somewhat alive. If not already enabled on the target asset, the attacker would have to achieve a modification of Edge settings to enable the “Allow sites to be reloaded in Internet Explorer” setting. Subsequent exploitation would involve convincing the user to open an Internet Explorer mode tab within Edge and then opening the malicious URL. Remediation involves patching Windows itself; all current versions of Windows are affected.
Microsoft Project: zero-day RCE
Rounding out this month’s half dozen exploited-in-the-wild vulnerabilities is CVE-2024-38189, which describes RCE in Microsoft Project. Exploitation requires that an attacker convince the user to open a malicious file, and is possible only where the “Block macros from running in Office files from the Internet” policy is disabled — it is enabled by default — and the “VBA Macro Notification Settings” are set to a low enough level. Happily, the Preview Pane is not an attack vector in this case.
Microsoft Office: zero-day spoofing
Published last week to acknowledge its public disclosure, and patched today for all current versions of Office, CVE-2024-38200 describes a spoofing vulnerability. Exploitation requires that the user click a malicious link. Although the advisory doesn’t describe the impact, the weakness is CWE-200: Exposure of Sensitive Information to an Unauthorized Actor, and the FAQ mentions outgoing NTLM traffic; reading between the lines, it’s highly likely that NTLM hashes are exposed upon successful exploitation.
The advisory suggests mitigating factors which may already apply, or which may prove helpful to improve security posture: adding users to the Protected Users Security Group, which prevents the use of NTLM authentication, and blocking outbound SMB connections to port 445. Both of these mitigation measures may break legacy authentication in some scenarios.
Somewhat unusually, Microsoft claims to have fixed this vulnerability twice, since in addition to today’s patches, an alternative fix was enabled via Feature Flighting on 2024-07-30 for all in-support versions of Office and 365. Microsoft still recommends that customers update to the 2024-08-13 patches to receive the final version of the fix. Somewhat confusingly, the FAQ then goes on to say that the Security Updates table will be revised when the update is publicly available; however, it’s likely that Microsoft will update the FAQ in the near future to clarify that a this was a minor FAQ editing oversight rather than a suggestion that further patches are expected.
Windows Line Printer Daemon: zero-day RCE
Line Printer Daemon (LPD) vulnerabilities are like buses: you wait ages for one, and then two come along in quick succession. Last month’s denial of service vulnerability is now joined by https://msrc.microsoft.com/update-guide/en-US/advisory/CVE-2024-38199, a publicly-disclosed RCE vulnerability. Exploitation requires that an attacker sends a malicious print task to a shared vulnerable Windows Line Printer Daemon service across the network. Many admins won’t need to worry about this vulnerability, since Microsoft has been encouraging everyone to migrate away from LPD for almost a decade, and it isn’t installed by default on Windows products newer than Server 2012. Still, patches are available for Windows Server 2008 SP2, Server 2022 23H2, and everything in between.
SharePoint & Exchange update
As something of an olive branch for defenders who may now be eyeing their to-do list with concern, Microsoft has not published any SharePoint or Exchange vulnerabilities this month.
Microsoft lifecycle update
All versions of Visual Studio for Mac retire on 2024-08-31 and will no longer receive any further updates — including security patches — after that date. The URL seems to anticipate that some people will have questions: https://learn.microsoft.com/en-us/visualstudio/mac/what-happened-to-vs-for-mac. Microsoft suggests the C# Dev Kit for Visual Studio Code as one possible alternative.
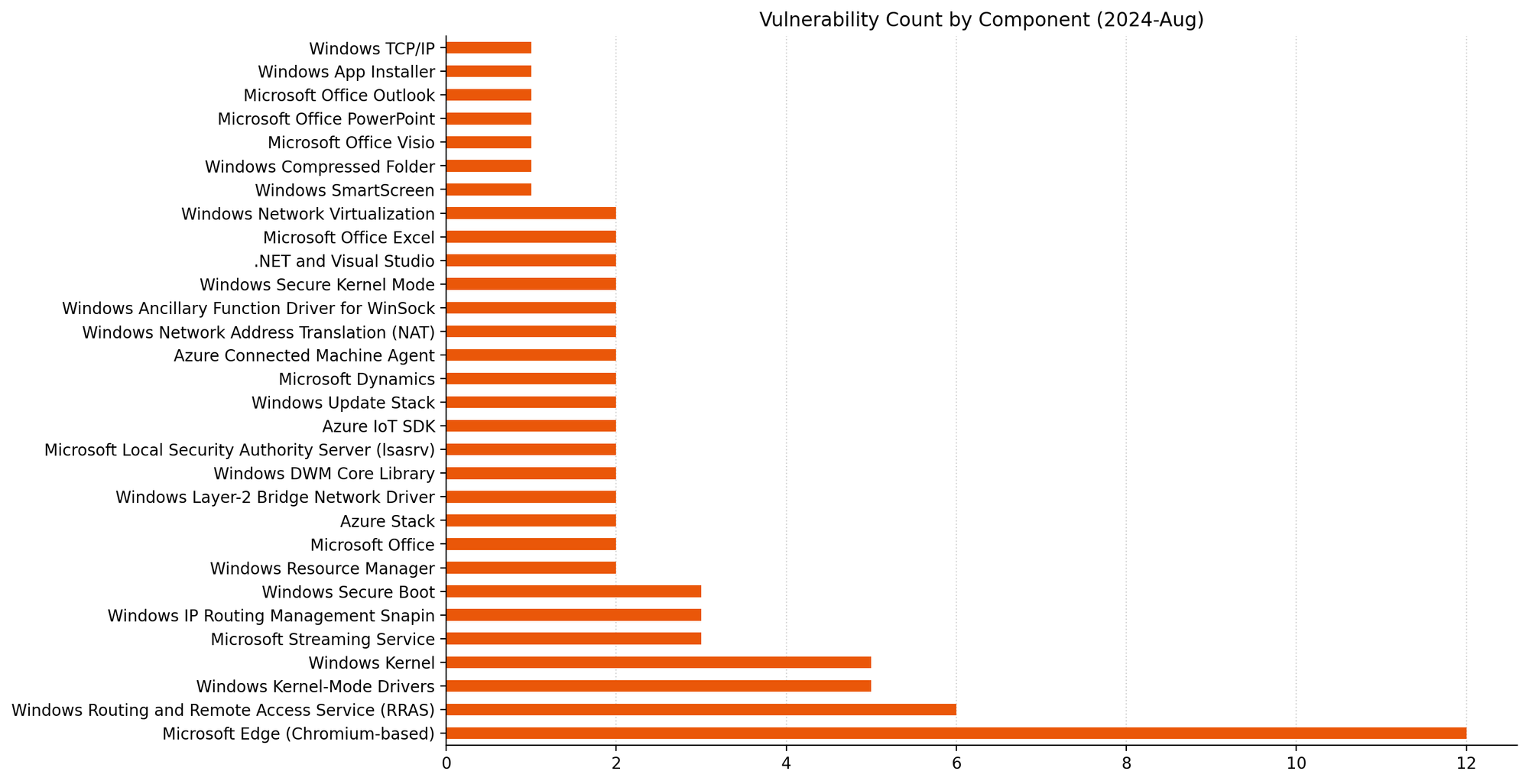
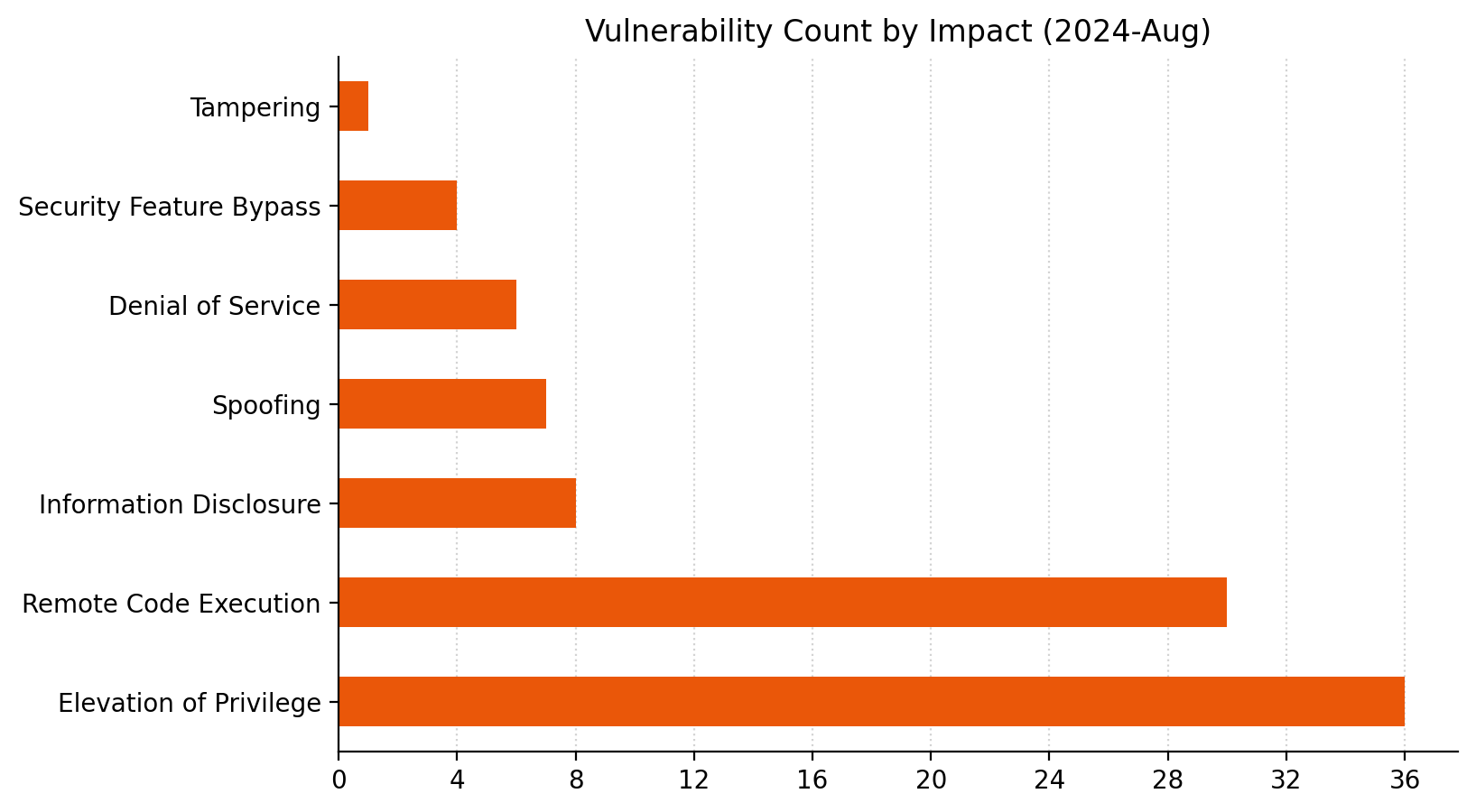
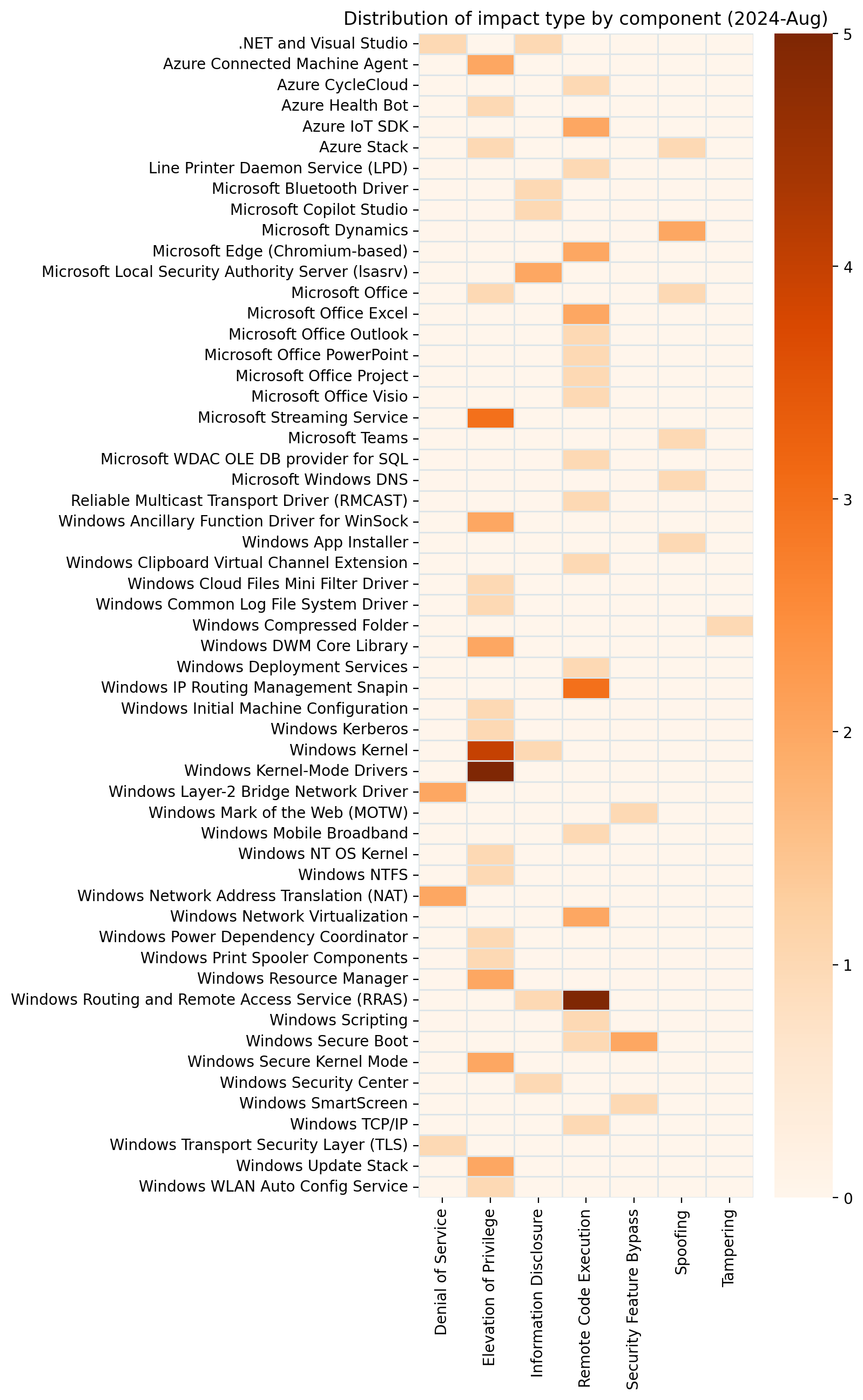
Summary Charts
Summary Tables
Apps vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38177 | Windows App Installer Spoofing Vulnerability | No | No | 7.8 |
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38108 | Azure Stack Hub Spoofing Vulnerability | No | No | 9.3 |
| CVE-2024-38109 | Azure Health Bot Elevation of Privilege Vulnerability | No | No | 9.1 |
| CVE-2024-38195 | Azure CycleCloud Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-38098 | Azure Connected Machine Agent Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38162 | Azure Connected Machine Agent Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38201 | Azure Stack Hub Elevation of Privilege Vulnerability | No | No | 7 |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38218 | Microsoft Edge (HTML-based) Memory Corruption Vulnerability | No | No | 8.4 |
| CVE-2024-38219 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability | No | No | 6.5 |
| CVE-2024-7536 | Chromium: CVE-2024-7550 Type Confusion in V8 | No | No | N/A |
| CVE-2024-7535 | Chromium: CVE-2024-7536 Use after free in WebAudio | No | No | N/A |
| CVE-2024-7534 | Chromium: CVE-2024-7535 Inappropriate implementation in V8 | No | No | N/A |
| CVE-2024-7533 | Chromium: CVE-2024-7534 Heap buffer overflow in Layout | No | No | N/A |
| CVE-2024-7532 | Chromium: CVE-2024-7533 Use after free in Sharing | No | No | N/A |
| CVE-2024-7550 | Chromium: CVE-2024-7532 Out of bounds memory access in ANGLE | No | No | N/A |
| CVE-2024-7256 | Chromium: CVE-2024-7256 Insufficient data validation in Dawn | No | No | N/A |
| CVE-2024-7255 | Chromium: CVE-2024-7255 Out of bounds read in WebTransport | No | No | N/A |
| CVE-2024-6990 | Chromium: CVE-2024-6990 Uninitialized Use in Dawn | No | No | N/A |
| CVE-2024-38222 | Microsoft Edge (Chromium-based) Information Disclosure Vulnerability | No | No | N/A |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38168 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38157 | Azure IoT SDK Remote Code Execution Vulnerability | No | No | 7 |
| CVE-2024-38158 | Azure IoT SDK Remote Code Execution Vulnerability | No | No | 7 |
| CVE-2024-38167 | .NET and Visual Studio Information Disclosure Vulnerability | No | No | 6.5 |
Mariner Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2022-2601 | Redhat: CVE-2022-2601 grub2 - Buffer overflow in grub_font_construct_glyph() can lead to out-of-bound write and possible secure boot bypass | No | No | 8.6 |
| CVE-2022-3775 | Redhat: CVE-2022-3775 grub2 - Heap based out-of-bounds write when rendering certain Unicode sequences | No | No | 7.1 |
Microsoft Dynamics vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38166 | Microsoft Dynamics 365 Cross-site Scripting Vulnerability | No | No | 8.2 |
| CVE-2024-38211 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability | No | No | 8.2 |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38189 | Microsoft Project Remote Code Execution Vulnerability | Yes | No | 8.8 |
| CVE-2024-38206 | Microsoft Copilot Studio Information Disclosure Vulnerability | No | No | 8.5 |
| CVE-2024-38171 | Microsoft PowerPoint Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-38084 | Microsoft OfficePlus Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38169 | Microsoft Office Visio Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-38172 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-38170 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.1 |
| CVE-2024-38173 | Microsoft Outlook Remote Code Execution Vulnerability | No | No | 6.7 |
| CVE-2024-38197 | Microsoft Teams for iOS Spoofing Vulnerability | No | No | 6.5 |
| CVE-2024-38200 | Microsoft Office Spoofing Vulnerability | No | Yes | 6.5 |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38159 | Windows Network Virtualization Remote Code Execution Vulnerability | No | No | 9.1 |
| CVE-2024-38160 | Windows Network Virtualization Remote Code Execution Vulnerability | No | No | 9.1 |
| CVE-2024-38163 | Windows Update Stack Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38142 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38135 | Windows Resilient File System (ReFS) Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38184 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38185 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38186 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38187 | Windows Kernel-Mode Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38133 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38150 | Windows DWM Core Library Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38215 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38147 | Microsoft DWM Core Library Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38148 | Windows Secure Channel Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38138 | Windows Deployment Services Remote Code Execution Vulnerability | No | No | 7.5 |
| CVE-2024-38202 | Windows Update Stack Elevation of Privilege Vulnerability | No | Yes | 7.3 |
| CVE-2024-38136 | Windows Resource Manager PSM Service Extension Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-38137 | Windows Resource Manager PSM Service Extension Elevation of Privilege Vulnerability | No | No | 7 |
| CVE-2024-38106 | Windows Kernel Elevation of Privilege Vulnerability | Yes | No | 7 |
| CVE-2024-38161 | Windows Mobile Broadband Driver Remote Code Execution Vulnerability | No | No | 6.8 |
| CVE-2024-21302 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability | No | Yes | 6.7 |
| CVE-2024-38165 | Windows Compressed Folder Tampering Vulnerability | No | No | 6.5 |
| CVE-2024-38155 | Security Center Broker Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-38123 | Windows Bluetooth Driver Information Disclosure Vulnerability | No | No | 4.4 |
| CVE-2024-38143 | Windows WLAN AutoConfig Service Elevation of Privilege Vulnerability | No | No | 4.2 |
Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score |
|---|---|---|---|---|
| CVE-2024-38063 | Windows TCP/IP Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-38140 | Windows Reliable Multicast Transport Driver (RMCAST) Remote Code Execution Vulnerability | No | No | 9.8 |
| CVE-2024-38199 | Windows Line Printer Daemon (LPD) Service Remote Code Execution Vulnerability | No | Yes | 9.8 |
| CVE-2024-38180 | Windows SmartScreen Security Feature Bypass Vulnerability | No | No | 8.8 |
| CVE-2024-38121 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38128 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38130 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38154 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38120 | Windows Routing and Remote Access Service (RRAS) Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38114 | Windows IP Routing Management Snapin Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38115 | Windows IP Routing Management Snapin Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38116 | Windows IP Routing Management Snapin Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2024-38144 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability | No | No | 8.8 |
| CVE-2024-38131 | Clipboard Virtual Channel Extension Remote Code Execution Vulnerability | No | No | 8.8 |
| CVE-2023-40547 | Redhat: CVE-2023-40547 Shim - RCE in HTTP boot support may lead to secure boot bypass | No | No | 8.3 |
| CVE-2024-29995 | Windows Kerberos Elevation of Privilege Vulnerability | No | No | 8.1 |
| CVE-2024-38107 | Windows Power Dependency Coordinator Elevation of Privilege Vulnerability | Yes | No | 7.8 |
| CVE-2024-38152 | Windows OLE Remote Code Execution Vulnerability | No | No | 7.8 |
| CVE-2024-38153 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38127 | Windows Hyper-V Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38196 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38193 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Yes | No | 7.8 |
| CVE-2024-38141 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38117 | NTFS Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38125 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38134 | Kernel Streaming WOW Thunk Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38191 | Kernel Streaming Service Driver Elevation of Privilege Vulnerability | No | No | 7.8 |
| CVE-2024-38198 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.5 |
| CVE-2024-38126 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38132 | Windows Network Address Translation (NAT) Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38145 | Windows Layer-2 Bridge Network Driver Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-38146 | Windows Layer-2 Bridge Network Driver Denial of Service Vulnerability | No | No | 7.5 |
| CVE-2024-37968 | Windows DNS Spoofing Vulnerability | No | No | 7.5 |
| CVE-2024-38178 | Scripting Engine Memory Corruption Vulnerability | Yes | No | 7.5 |
| CVE-2024-38223 | Windows Initial Machine Configuration Elevation of Privilege Vulnerability | No | No | 6.8 |
| CVE-2024-38214 | Windows Routing and Remote Access Service (RRAS) Information Disclosure Vulnerability | No | No | 6.5 |
| CVE-2024-38213 | Windows Mark of the Web Security Feature Bypass Vulnerability | Yes | No | 6.5 |
| CVE-2024-38151 | Windows Kernel Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-38118 | Microsoft Local Security Authority (LSA) Server Information Disclosure Vulnerability | No | No | 5.5 |
| CVE-2024-38122 | Microsoft Local Security Authority (LSA) Server Information Disclosure Vulnerability | No | No | 5.5 |
Source: Rapid7
Source Link: https://blog.rapid7.com/2024/08/13/patch-tuesday-august-2024/